Silent Crypto Heist: Hackers Hijack Thousands of PostgreSQL Servers in Stealthy Mining Spree
Massive Cybersecurity Breach: Over 1,500 PostgreSQL Servers Hijacked for Crypto Mining
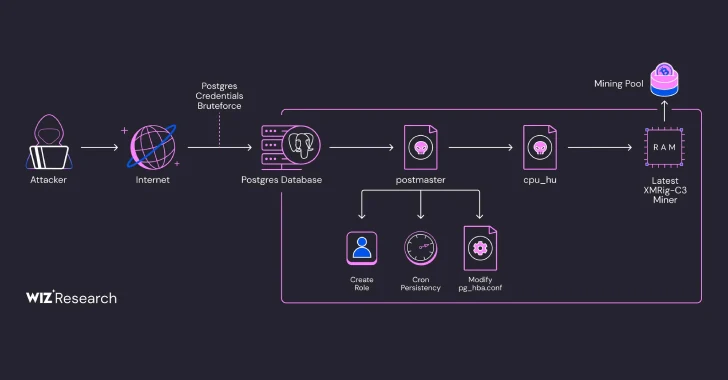
Cybersecurity researchers have uncovered a widespread attack targeting PostgreSQL database servers, revealing a sophisticated campaign that exploits weak credentials and SQL vulnerabilities to launch fileless cryptocurrency mining operations.
The massive breach involves more than 1,500 PostgreSQL servers worldwide, demonstrating the critical importance of robust security practices in database management. Attackers are leveraging simple yet effective techniques to gain unauthorized access, primarily targeting servers with weak or default login credentials.
How the Attack Works
The hackers employ a cunning approach that bypasses traditional detection methods. By exploiting weak authentication and using advanced SQL injection techniques, they infiltrate database servers and deploy fileless malware designed to mine cryptocurrency without leaving significant traces.
Key Risks and Implications
This attack highlights several critical cybersecurity concerns:
- Widespread vulnerability of poorly secured database servers
- The growing threat of cryptocurrency mining malware
- The importance of strong, unique credentials
Recommended Protection Strategies
To safeguard against such attacks, organizations should:
- Implement strong, complex passwords
- Enable multi-factor authentication
- Regularly update and patch database systems
- Monitor for unusual database activities
As cryptocurrency mining attacks continue to evolve, vigilance and proactive security measures remain paramount in protecting digital infrastructure.
